Picture this – it’s the year 2035 and the headline has finally hit – “Quantum computing is now.”
Since quantum advantage was won in 2030, the flow of innovations began as commercially viable quantum compute now spills across businesses. Vaccine and drug simulations revolutionize human and animal testing, new LLMs are being trained at high speed and more accurately than ever before. Our leading financial institutions have noted record data speeds and numbers of bumper trade deals and transactions processed, and the world celebrates as a new CO2 catalyst has been discovered to recycle carbon dioxide into hydrogen.
But, over the weeks that follow what’s been dubbed the “Summer of Quantum Success,” the number of stably-formed qubits in a quantum computer reach 4099, and around the world, the cyber-attacks begin as our public key encryptions crack under Shor’s algorithm. This eventful day comes to be known as “Q-Day.”
Data set after data set is unveiled, unraveled and distorted, or else held hostage for billions of dollars ransom. Historical data harvested well before Q-Day undergoes a series of damaging leaks, bringing down enterprises. Amidst the turmoil, a select few organizations remained safe, cushioned by the quantum-safe, cyber agile algorithms they had finished updating just in time after a decade of preparations.
Now you might say imagination has overrun journalism here, but there’s no doubt that a future powered by quantum computing is set to be world-changing. Not too dissimilar to the hype cycle around AI, the excitement around the upcoming capabilities of quantum computing is fast approaching its apex. Fully commercially viable quantum, as well as encryption cracking quantum, are still a good few years away in theory, but experts from IBM, Deloitte and Accenture are speaking loud and clear that quantum readiness needs to begin now.
At the peak of the hype cycle
Hype aside, there are some realistic use cases for quantum computing abilities we will hopefully see in the next few years which will be colossal for our planet and our lives. The initial sweet spot of use cases will be simulations and calculations that don’t require fast below millisecond response turnaround, and areas like modeling at the molecular level with quantum.
Richard Hopkins, distinguished engineer and senior quantum ambassador at IBM, shares the likely realities of early quantum commercial viability: “I’m expecting that there are enough high-value use cases, ones that don’t require millisecond turnarounds like in Visa and the MasterCard of payment type scenarios, where if we’re trying to optimize the flow of energy around the planet, biotech tankers or whatever, that’s a problem that you could probably look at once a day, rather than trying to do it within a millisecond.”
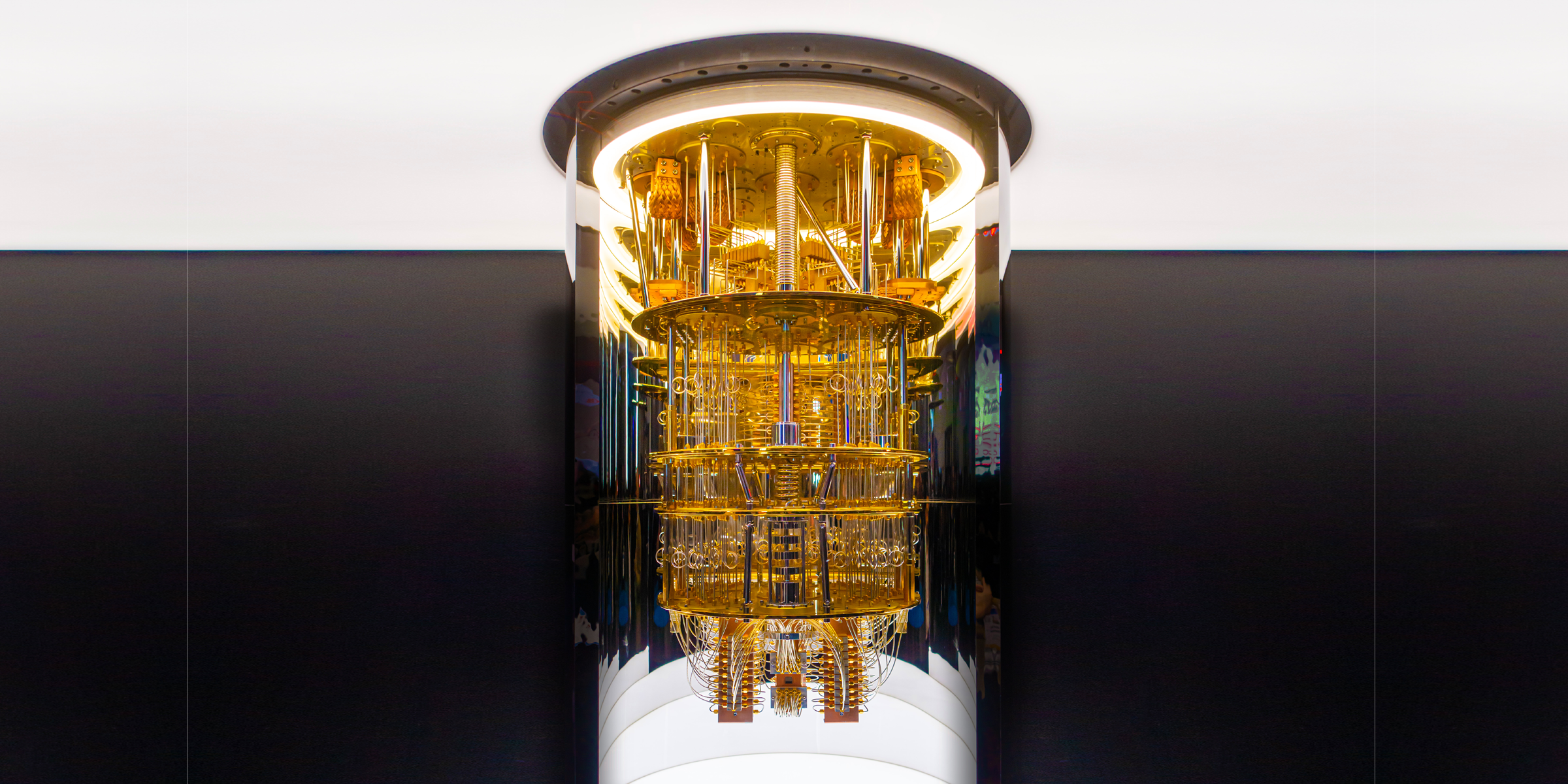
At the moment, maintaining qubits for usable periods of time is still a blocker for many use cases. One goal for IBM, besides continuing to grow the number of qubits in their quantum machines, is to create a cloud-based server farm with multiple quantum processing units (QPUs), protecting from outages and alleviating the need for a total reset, recalibrate and read if there is a disturbance in one of the superconducting method cylinders.
True commercial viability of quantum computers across the world is still a few years away, with 2030 often touted as the expected timeline, though some are anticipating sooner. Microsoft has partnered with quantum hardware companies Quantinuum, IonQ and Rigetti to provide cloud access to quantum hardware with 23 fully connected qubits and Amazon has acted similarly to deliver its own Amazon Braket quantum tools. IBM currently has one 433 qubit machine, Osprey, sitting out there on the web today and it’s also announced an upgrade to the 24 other machines available for users, ramping up that entire fleet to 127 qubits, its Eagle processor. Many of these have free fees for academia and right now IBM Quantum’s Composer is free to play with and build, visualize and run quantum circuits on quantum hardware or simulators.
In a measured approach, Hopkins is quick to state that though he suspects IBM is in the lead for quantum computing research with the most amount of qubits, there is a way to go before claiming quantum advantage (aka commercially viable quantum): “It’s going to require some new science and some new maths and a lot of research and maybe even a large supercomputer to be able to fully verify what we’ve done has been absolutely right. We want to claim it when we know that we can demonstrate that it has produced the right result in a real-world context that no conventional computer has ever been able to solve within a reasonable timeframe.
“There’s so much competition in the field. Superconducting, ion trap, photonic and others, they’re all at different stages of evolution, and they all have their strengths and weaknesses. I’d certainly not be surprised to see multiple quantum technologies succeed with different techniques being used for certain kinds of problems. But I think where the frustration will kick in is that we can’t get it everywhere all at once. There’s still a way to go on the engineering before we can change the world and change the planet. It is going to take a bit more time. As an engineer, that’s going to be annoying.”
There’s still a way to go on the engineering before we can change the world and change the planet – Richard Hopkins, IBM
It’s a similar outlook for Scott Buchholz, CTO of Deloitte’s government practice and global quantum computing lead, as he shares that quantum is set to have a softer launch than we might expect: “I think people have this impression that we’re going to wake up one morning and quantum computers will have taken over the world. But the challenge is, if we look on [to] January 1, 2030, what would the world have to look like for people to feel like the transition had happened? In the next few years, we might start seeing niche problems where quantum computers can do better than classical computers. And two years later, there will be yet more problems that are better solved with quantum computers, and so on.
“I think people conceptually think there’s going to be a light switch or a Frankenstein switch. It’s going to be more gradual than that, it’s not going to be quite as dramatic as people think.”
Buchholz uses the example of the slow introduction of digital cameras into the mass market, and arguably you can also draw a similar parallel to the advancement of AI, as both plotted paths from niche and inaccessible use cases to becoming more readily available for everyday and commercial use.
Yet, despite the predicted slow burn of quantum benefits, what remains more pressing at the top of experts’ to-do lists is sharing the graver concerns around quantum risk.
Quantum risks will break today’s cybersec
In the mission to continuously grow the number of qubits available for powering larger and faster calculations, it’s predicted that as the number of qubits strikes the quantum-defining figure of 4099, the machines will have the negative side effect of being able to implement an algorithm to crack our current public encryption algorithms, and perhaps much of our distributed ledger technology too, rendering the majority of our cyber security systems to date wide open for hackers.
For IBM’s Hopkins, this has been a concern to beat since last decade: “Staying cybersecure with quantum – that’s all about people understanding it’s a genuine threat in the first case. When I first told people about this, back in 2016, people just looked at me and went ‘you’re kidding’.
“The timeframe for when quantum computers start doing bad things, the kind of cyber issues such as breaking cryptography, breaking the stuff that underpins our daily lives now, that is looking like potentially somewhere between 2030 and 2035.”
Not only that, but a growing trend of stealing now to decrypt later is emerging, where despite being unable to access the data now, actors are harvesting today’s confidential data so that when the technology is ready, it can be hacked in the future. It’s prompted a kind of modern-day space race of sorts, where perhaps nations and organizations are investing rapidly to reach viable quantum first.
Dr Colin Soutar, Deloitte’s managing director of cyber and strategic risk products and technology for US Government and public services explains: “There’s a narrative that there are some nation states, and corporations for corporate secrets as well, that are purportedly stealing data today in the anticipation that they were able to break it tomorrow. It’s called ‘harvest now, decrypt later’. It is likely the nation states will get into that sort of discourse in terms of actively trying to develop ahead of each other. But also, there is the thought that corporations, you know, have similar interests as well.”
Thankfully, however, there are currently solutions, with a range of counter-algorithms available that the big quantum firms claim to be resistant to quantum-powered hacking.
IBM’s Hopkins, for one, shares: “Now, we have four quantum-safe algorithms, approved through a competition, and we’ve been rolling out quantum-safe stuff very seriously. What’s the next target for the hackers? Well, they’ll probably be looking to get anything on the mainframe because that’s where most of the world’s financial data still resides and everything else, so we’ve put quantum safe algorithms into the z16 [mainframe computer from IBM] and we’ve put it onto our cloud. So we’re rolling this stuff out pretty incrementally and pretty quickly, actually.
“The greatest minds in the world have come up with a new way that doesn’t rely on factoring and relies on something called lattice, which is a different way to weave in a shared secret and sort of perform the same function, but with different math. So that will stand up to a quantum computer no matter how big it gets, because it doesn’t rely on what a quantum computer can do well.”
Nonetheless, as Hopkins states, it presents businesses with a new kind of dilemma many have yet to encounter.
“We’ve been very lucky, frankly, that we’ve had very stable cryptographic environments that haven’t needed to change,” says Hopkins. “All we need to do is increase the key length for the last 40 to 50 years. But now we’re beginning to realize that as quantum computers come along, we definitely need to check the algorithms.”
Who’s acting now and how?
Though expectantly specific customer names can’t be shared, Big Tech names have said that leading financial institutions and governments are starting to take next-step actions increasingly seriously, and with some industries built entirely on cryptography, such as telecommunications, we are looking at entire industry reengineering for the goal of becoming “quantum safe”.
To create cyber protection beyond the likes of quantum risk, businesses’ next steps look to reach for cyber agility, a more flexibly updateable cybersecurity model, to enable a faster update to their security systems in the future. Historically, examples of the time taken to update security models lie in the decade bracket, and the big names are advising that this current update for quantum readiness could take around eight years.
Time is surely ticking, and action is needed a lot faster than the predicted 2035 deadline might suggest. The likes of IBM, Deloitte and Accenture, among others, are working with industry bodies to speed up that movement.
We know the race is on. The whole concept of the way we do public key encryption needs to be changed – Tom Patterson, Accenture
Accenture is currently advising every business to develop a quantum security plan as part of their five-year security plan, and Tom Patterson, Accenture’s global lead for quantum security and space security, shares: “It’s certainly a question that comes up in every business meeting I work in – when will the newspaper headline be ‘Quantum computers can now decrypt all of your secrets’? Because we know that the race is on. The whole concept of the way we do public key encryption needs to be changed, the math needs to be traded. And the only question is, are you, the organization, going to implement the solution before that headline appears? Are you going to do it the day after, when you’re at huge risk that your whole business could be shut off and be in scramble mode?
“We put in a system so that algorithms can be rotated easily. That’s what governments are moving towards and that’s what a lot of the large financial organizations are moving towards. In the UK, you look at GCHQ – what they’re saying is we need to fix our systems right now. In the US, it’s the NSA, the White House with executive orders. They’re acknowledging the same messages.
“We really strongly believe that there are good answers for this. It’s not a big scary ‘we’re in trouble and there’s nothing you can do’; it’s really that this change is coming, it’s going to be a big risk but there’s something you can do – and it’s not cost prohibitive and it doesn’t require magic – it just requires action.”
Speaking for IBM, Hopkins is clear that as amazing as the support for quantum technologies is, there is ongoing need for greater action: “We’re working very closely with GSMA and a few other industry bodies there to make that movement start to happen. I don’t think the US government’s woken up to it and I don’t think UK government has quite managed to understand the threat fully. The UK government is very excited about the quantum strategy and investing £2.4bn into quantum technologies. We have to understand that push forwards on technology comes with a downside; you’re going to have to sort out the cryptographic systems in time for 2035 at the latest. But these are about three-year programs to even get to the point where you know what you need to do first – these are fairly major things.”
However, industry standards don’t currently contain this upgrade requirement, with next year set for the National Institute of Standards and Technology to redefine these regulations. That’s not to mention the upheaval involved, with perhaps the need for incentives and greater assistance to get organizations started on the long upgrade journey.
With uncertain timeframes surrounding quantum, Deloitte’s Soutar suggests that some organizations are hesitant to act over security updates, despite the security position from the World Economic Forum’s reports stating to kickstart actions now.
If a nation state has a quantum computer that wants to attack cryptography, they’ll use it pretty quickly – Dr Colin Soutar, Deloitte
Soutar explains: “Our story is be cautious. If you wait four years, it’s going to take eight years to do all your upgrades. For quantum computing, there won’t be a light switch that will flick one day but you can bet if there’s a nation state that has a quantum computer that wants to attack cryptography, they’ll use it pretty blindly, and pretty quickly. So if that’s ten years out, and you’re still doing your upgrades, then that’s a huge problem, right?
“The first steps really talk about discovery. Where are your cryptographic algorithms today? How much is in-house? How much are you relying on third-party and your suppliers to provide? What data are you protecting? What communications are you protecting using cryptography? And once you’ve got a sense of that inventory, then you can start to think about what does it mean to be what people are calling “crypto agile”, and run things in parallel or quickly do an update to another system.”
A balanced quantum lens offers us a change of tact
From some of the world’s most influential quantum computing experts, the message is that the race is not resting on the fastest nation or organization to reach commercially viable quantum advantage, but rather on businesses to succeed in protecting themselves in time for the quantum cyber security threat and then be able to continue gaining the use case benefits.
With the size of these projects no doubt seeming insurmountable to some, it calls into question the enterprise approach to data collection over the past decade as businesses now start to shift into cyber agility. Contrary to the mass data grab we’ve been experiencing over the past five, ten years, with the more data mentality, wherein the more we have, the more we can process and the better we can run our businesses, Deloitte is instead encouraging people to rethink the data they keep on tap.
Buchholz says: “It’s just good cyber hygiene that needs to be done. I’m hopeful that there are two consequences of this quantum lens. One is that better cyber hygiene around cryptography in general, regardless of the quantum threat or not. Secondly, I think it will make organizations in the commercial and the government sectors think twice about the data that they are storing and whether they really need it or not, because again, you can’t steal data that’s not available.”
I’m hopeful a quantum lens will make organizations think twice about the data that they are storing – Scott Buchholz, Deloitte
And beyond Buchholz’s cyber hygiene benefits, there are also the storage costs, both monetary and environmental to consider, where we have been holding on to so much unused but perhaps potentially risky data.
Regardless of the risks involved with potential bad quantum actors, technologists also remain optimistic that beyond the far-flung ideals of the hype cycle, quantum compute will still have ongoing groundbreaking benefits that will outweigh the cyber risk negatives.
Accenture’s Patterson covers this neatly in saying: “It’s really going to change the world… Quantum communications will be running by the end of this decade; quantum computers are already available in clouds that you can use. The winner is really humanity and I fully support the continued global efforts to try and push the science because it’s to everyone’s benefit.”